1
Patch Tuesday| Updates | Security | Privacy | Anti-virus / This "Windows 11 24H2" update download can quietly steal your sensitive data
« Last post by javajolt on April 13, 2026, 11:54:27 PM »The malicious 24H2 update download website is able to evade detection from anti-virus and other boot-time security on Windows 11.
 Neowin readers are well aware of how legit Windows 11 updates can break important features and functions like Start menu Search and PC reset option; however, malicious forged ones can be even more deadly. One such fake Microsoft support website has been tricking users into installing a malicious Windows update that silently steals sensitive data, according to new research published by Malwarebytes.
Neowin readers are well aware of how legit Windows 11 updates can break important features and functions like Start menu Search and PC reset option; however, malicious forged ones can be even more deadly. One such fake Microsoft support website has been tricking users into installing a malicious Windows update that silently steals sensitive data, according to new research published by Malwarebytes.
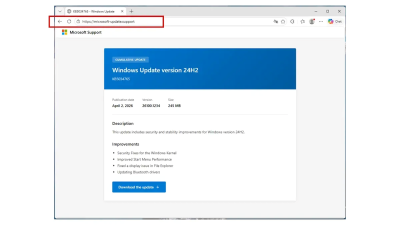
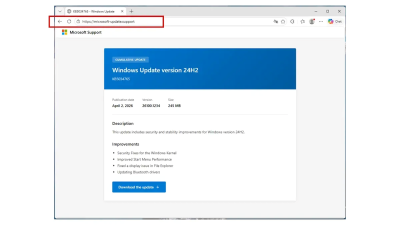
The cybersecurity firm notes that the campaign is being carried out by a convincing phishing site hosted on a typosquatted domain designed to mimic official Microsoft support pages. The attack targets Windows users mainly in France by offering what appears to be a legitimate cumulative update for Windows 11 24H2. Coincidentally, the French government just decided to dump Windows in favor of Linux, and although likely unrelated, we wonder if that has any connection.
According to the researchers, the site "microsoft-update[.]support" presents a familiar UI and color scheme, complete with a fake knowledge base (KB) reference and a prominent "Download the update" button. Users who click it receive an 83MB installer file labeled WindowsUpdate 1.0.0.msi, that appears indeed authentic at first glance. Observant ones will notice in the image below, that the update being delivered, "KB5034765", was actually released back in February 2024 for Windows 11 23H2 and 22H2, not for 24H2.
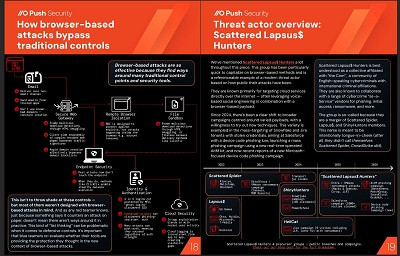
 The attack also uses trustworthy technologies to mask the real intent. The installer is built using WiX Toolset, a widely used open-source framework, and deploys an Electron-based app, effectively a Chromium browser shell, to execute the payload. This layered approach helps the malware evade antivirus detection. Malwarebytes notes zero detections recorded across dozens of security engines at the time of analysis as the executable itself is clean.
The attack also uses trustworthy technologies to mask the real intent. The installer is built using WiX Toolset, a widely used open-source framework, and deploys an Electron-based app, effectively a Chromium browser shell, to execute the payload. This layered approach helps the malware evade antivirus detection. Malwarebytes notes zero detections recorded across dozens of security engines at the time of analysis as the executable itself is clean.
Once executed, the installer launches a Visual Basic script that triggers the Electron app, which in turn spawns a disguised Python process. This process installs multiple packages commonly associated with data theft, including tools for encryption, system inspection, and deep Windows API access. The malware then begins harvesting sensitive data as Malwarebytes found it can extract browser-stored credentials, Discord tokens, and capture payment-related information.
To maintain persistence, the malware has devised several things in its favor including a registry entry disguised as an actual Windows security component and a startup shortcut pretending to be a Spotify app .lnk launcher. This approach ensures the malware survives system reboots with minimal suspicion.
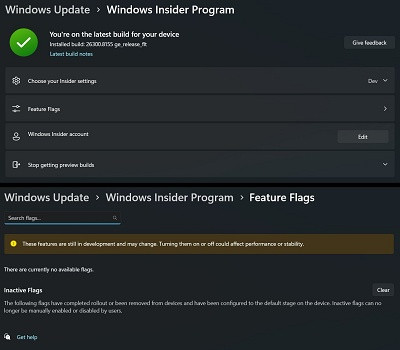
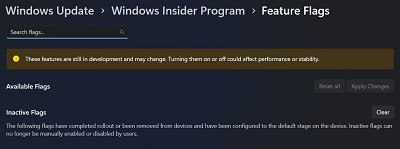
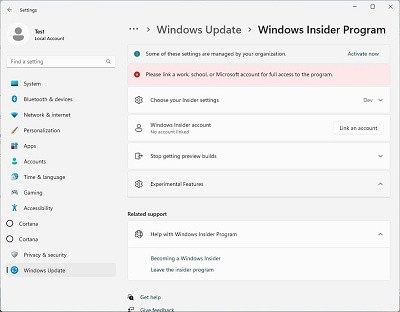
Users are advised to install updates only through official Windows Update settings or trusted Microsoft domains. You can also follow Neowin as we cover these updates and link to official, secure Microsoft sites only, or reputable third-party apps. Any standalone update downloads from an unfamiliar website should be treated as suspicious and with extreme caution. You can find more technical details in the original blog post here on Malwarebytes' website.
source
The cybersecurity firm notes that the campaign is being carried out by a convincing phishing site hosted on a typosquatted domain designed to mimic official Microsoft support pages. The attack targets Windows users mainly in France by offering what appears to be a legitimate cumulative update for Windows 11 24H2. Coincidentally, the French government just decided to dump Windows in favor of Linux, and although likely unrelated, we wonder if that has any connection.
According to the researchers, the site "microsoft-update[.]support" presents a familiar UI and color scheme, complete with a fake knowledge base (KB) reference and a prominent "Download the update" button. Users who click it receive an 83MB installer file labeled WindowsUpdate 1.0.0.msi, that appears indeed authentic at first glance. Observant ones will notice in the image below, that the update being delivered, "KB5034765", was actually released back in February 2024 for Windows 11 23H2 and 22H2, not for 24H2.
Once executed, the installer launches a Visual Basic script that triggers the Electron app, which in turn spawns a disguised Python process. This process installs multiple packages commonly associated with data theft, including tools for encryption, system inspection, and deep Windows API access. The malware then begins harvesting sensitive data as Malwarebytes found it can extract browser-stored credentials, Discord tokens, and capture payment-related information.
To maintain persistence, the malware has devised several things in its favor including a registry entry disguised as an actual Windows security component and a startup shortcut pretending to be a Spotify app .lnk launcher. This approach ensures the malware survives system reboots with minimal suspicion.
Users are advised to install updates only through official Windows Update settings or trusted Microsoft domains. You can also follow Neowin as we cover these updates and link to official, secure Microsoft sites only, or reputable third-party apps. Any standalone update downloads from an unfamiliar website should be treated as suspicious and with extreme caution. You can find more technical details in the original blog post here on Malwarebytes' website.
source

 Recent Posts
Recent Posts