 PayPal has confirmed a data breach impacting PPWC loan users.
PayPal has confirmed a data breach impacting PPWC loan users.
SOPA Images/LightRocket via Getty ImagesUpdated February 22 with details of previous PayPal security incidents and warnings, further advice for those impacted by the confirmed PayPal Working Capital data breach, which prompted transaction refunds and account password resets, and as a statement from a PayPal spokesperson.
Some PayPal users have started to receive email from the company confirming a data breach that exposed personal information to a threat actor who gained access to PayPals systems, leading to some seeing unauthorized transactions on their accounts and the resetting of passwords. Heres what you need to know.
Data Breach Exposed Some PayPal Customer Data For Six MonthsA breach notification letter, which I have verified myself, has confirmed that some PayPal users have been impacted by a data breach after a hacker gained access to PayPal systems on July 1, 2025. The hacker apparently had access until December 12, 2025 when PayPal discovered the security incident. The breach, according to the notifications, which are dated February 10, impacted some users due to an error in its PayPal Working Capital (PPWC) loan application.
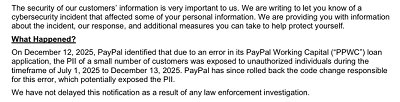 Excerpt from PayPal breach notification email.
Excerpt from PayPal breach notification email.
PayPalIt remains to be seen how the attacker access evolved, of course, as this remains something of a developing story and PayPal has yet to explain this in any detail beyond a code change being responsible. However, following publication of this article, a PayPal spokesperson provided the following statement: When there is a potential exposure of customer information, PayPal is required to notify affected customers. In this case, PayPals systems were not compromised. As such, we contacted the approximately 100 customers who were potentially impacted to provide awareness on this matter.
I am currently awaiting clarification regarding the seeming disparity between the statement saying that PayPals systems were not compromised, and the notification, which stated that following an investigation, the company had terminated the unauthorized access to PayPals systems. I will add another update if and when such a clarification is forthcoming.
 PayPal breach notification.
PayPal breach notification.
PayPalUpon learning about this unauthorized activity, we promptly began an investigation and took action to address this incident, including by taking steps to prevent unauthorized actors from obtaining further personal information, the PayPal notification stated. It would, however, be nice to know why it took a whole six months for PayPals security team to notice the exposure to unauthorized individuals, as mentioned in the breach notification itself. Thats a huge window of opportunity for attackers, and we should be grateful that so few accounts were potentially impacted before it was closed for good.
What Information Was Accessed By The PayPal Hacker?What we do know, at this point, however, is that the following information was potentially accessed:
Name
Email address
Phone number
Business address
Social Security number
Date of birth
PayPal has also confirmed that a few customers experienced unauthorized transactions on their account, and we now know that this was a very small number, 100 according to the spokesperson who contacted me. PayPal confirmed that it has already issued refunds to those customers who were impacted.
I mean, its great that such a relatively small number of PayPal users were affected by this incident, but the nature of the information that was potentially accessed is such that I would be greatly concerned about the opportunity it provides for any attacker to exploit with the use of further, unrelated to PayPal specifically, threats. Small businesses can be especially susceptible to phishing threats, especially those that are carefully and specifically targeted at them using such information. As such, I would advise all readers to take note of the PayPal security recommendations at the end of this article, whether impacted by this incident or not. It will only take a minute or two of your time, but could be one of the best investments your business has made.
This Is Not The First PayPal Security Warning RodeoI have covered many previous PayPal security warnings, which have mostly concerned phishing attacks delivered by email, text, or phone, although, if you stretch back as far as 2023, there was another breach. I reported on this at the time, confirming that a total of 34,942 PayPal accounts had been accessed by attacks using a credential stuffing attack methodology. Such attacks involve threat actors deploying an automated process in an attempt to access accounts with login credentials that have been compromised in some way, often credentials that have been reused between accounts and subsequently breached at one of them. Lists of such breached credentials are readily available on the dark web.
In December, 2025, I reported how attackers were using legitimate infrastructure to bypass email authentication protections when delivering malicious messages disguised as genuine PayPal support communications. On this occasion, the PayPal billing subscriptions feature was being abused by hackers in an attempt to steal your user account credentials. At the time, a PayPal spokesperson told me: PayPal does not tolerate fraudulent activity, and we work hard to protect our customers from consistently evolving phishing scams. We are actively mitigating this matter, and encourage people to always be vigilant online and mindful of unexpected messages. If customers suspect they are a target of a scam, we recommend they contact Customer Support directly through the PayPal app or our Contact page for assistance.
Just a few weeks earlier, I covered how a genuine PayPal email address was being used to deliver an invoice in what became known as the do not pay, do not phone attack. The fake invoice was for a larger purchase that the user had not actually made; this was the bait. The hook was a fake PayPal telephone support number to call in order to put a halt to the payment while a dispute was investigated. This was what is called a TOAD attack: Telephone-Oriented Attack Delivery involving seemingly official documents, urgency leverage and an adversary-controlled phone number. PayPal was not, and is not, sitting back and doing nothing; it has explained to me that it responds to the continual evolution of scamming tactics and methods, taking measures such as a combination of manual investigations and technology to prevent fraud, including proactive actions like limiting scam accounts or declining risky transactions.
PayPal Has Terminated Attacker Access And Reset Account PasswordsPayPal has stated that it has already terminated the attackers access to its systems, and those impacted (who should have received a notification email by now) have had their account passwords reset. This means that you may find that you are required to set a new password when you try to log in next.
We are offering you two years of complimentary credit monitoring and identity restoration services through Equifax, PayPal added, which will be of cold comfort to anyone impacted, I suspect.
PayPal Security RecommendationsThe breach notification also contained recommendations for those affected by the incident in the form of general security best practices. As such, these are a timely reminder for all PayPal users, not just the 100 impacted by the PayPal Working Capital breach, on how to be as safe as possible when using their accounts and the broader internet.
Use a unique username and password combination for every website and service.
I would agree that usernames are often overlooked, and we are all guilty of using the same email address for everything, but unique usernames add an extra layer of protection when it comes to credential stuffing attacks. Unique and complex passwords are a given, and you can take a password hacking test to see how yours fare.
Change your password and any associated security questions if you detect any suspicious activity on your account.
Again, sage advice that takes seconds to execute but could save you hours of hassle if your account is being compromised.
When links are present in an email, you should hover your mouse over the links to view the actual destination URL and should not click on the link if you are unsure of the destination URL or website.
Generally sound advice, although there are ways that attackers can obscure true destinations despite this. The better advice, in my never humble opinion, would be do not click links in emails or text messages and always visit a site using your browser and a known URL.
Pay attention to messages that promote urgency and require immediate action. If you are unsure or want to confirm the authenticity of urgent messages, you should visit PayPal and access your account to view any messages.
100% correct. You should always verify any such claims by visiting your account, using your browser and trusted links, which will reveal if what is being said has any truth to it. Only ever follow up with the stated support methods from the site itself.
PayPal will never ask you to provide the username and password of your PayPal account or any authentication factors, such as a one-time code, over a call, text, or an email message.
Dont panic, follow the previous advice, and dont give your details over the phone or in an email. Its common sense, so follow it whether regarding PayPal or any other online account.
I would add one critical recommendation that is missing from the list: use a passkey wherever the option is available.
Although this data breach does not appear to have impacted many users, PayPal has stated that customers should remain vigilant and review their account information and transaction histories.
source